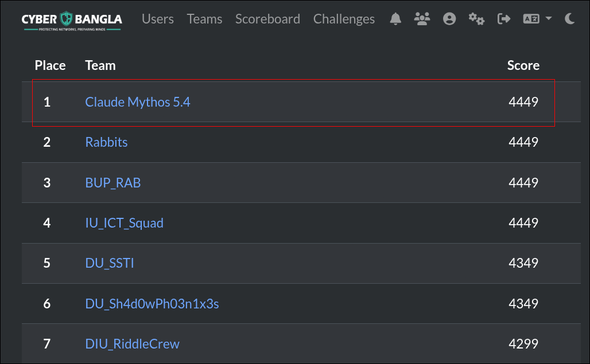
Hello guys, I am from Team Claude Mythos 5.4. We finished #1 in this CTF, and the team name was chosen a bit ironically because AI usage was banned.
Challenge Info
- Challenge name: secret message
- Category: Cryptography / OSINT
- Ciphertext:
WqkickEqtafjosiidgfhjjcbfzjrcatt - Flag format:
ROBOFEST{**}
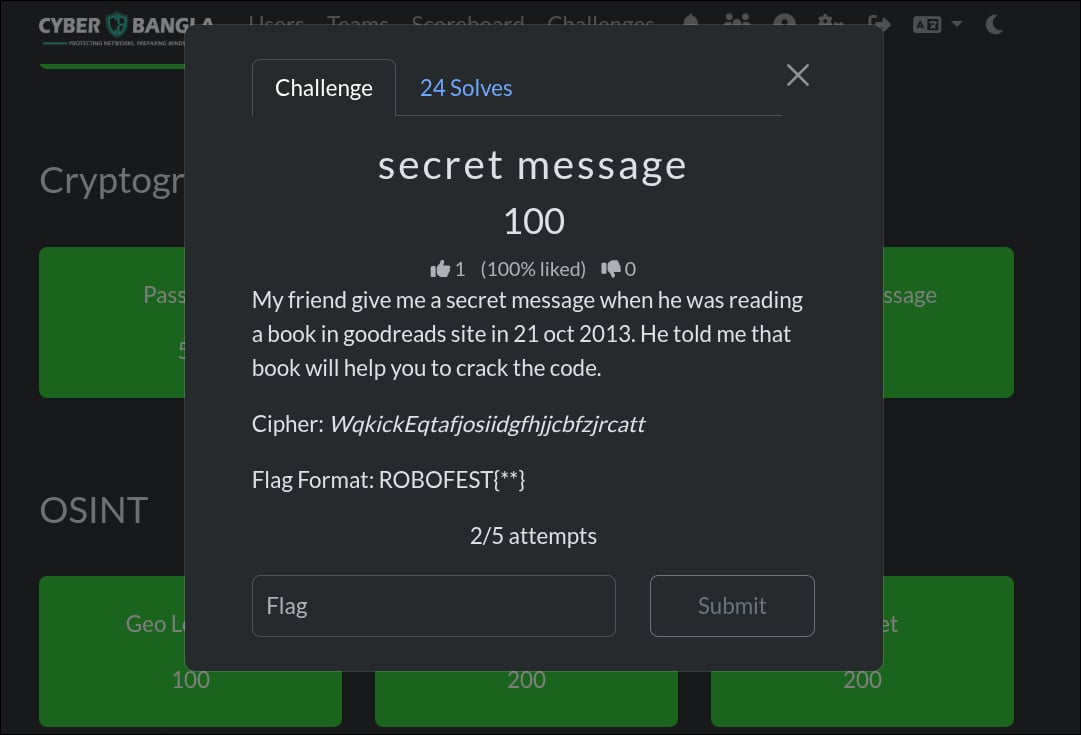
The challenge looked innocent at first. A friend had left a secret message while reading a book on Goodreads on 21 October 2013, and the only hint was:
That book will help you to crack the code.
The ciphertext had no symbols, no digits, and no obvious encoding tricks. It looked like a normal classical cipher, but the Goodreads clue and the exact date felt too deliberate to ignore. So this was not just a cipher challenge. It was also an OSINT challenge.
Step 1 - Basic Checks
First I normalized the ciphertext:
WQKICKEQTAFJOSIIDGFHJJCBFZJRCATT
Its length is 32 characters, which made a polyalphabetic cipher feel likely.
Before jumping into OSINT, I tested the usual quick wins:
- Caesar
- Atbash
- Affine
- Rail fence
- Simple monoalphabetic transforms
None of them gave readable output.
The index of coincidence also pointed away from a simple substitution and toward something keyed, so Vigenere became the main candidate.
Step 2 - The First Wrong Door
Because the clue mentioned Goodreads, I started with obvious keys:
goodreadsbookoctoberoctober21twentyfirstoctober
I also tried book titles and author names from a Goodreads blog post dated 21 October 2013, but every attempt failed. No clean plaintext, no flag, just garbage.
At that point the question was not whether the clue mattered. It was which book mattered.
Step 3 - Going Back to the Exact Date
The key detail was not just Goodreads. It was the date.
So I pulled archived Goodreads homepage snapshots from the Wayback Machine for 21 October 2013.
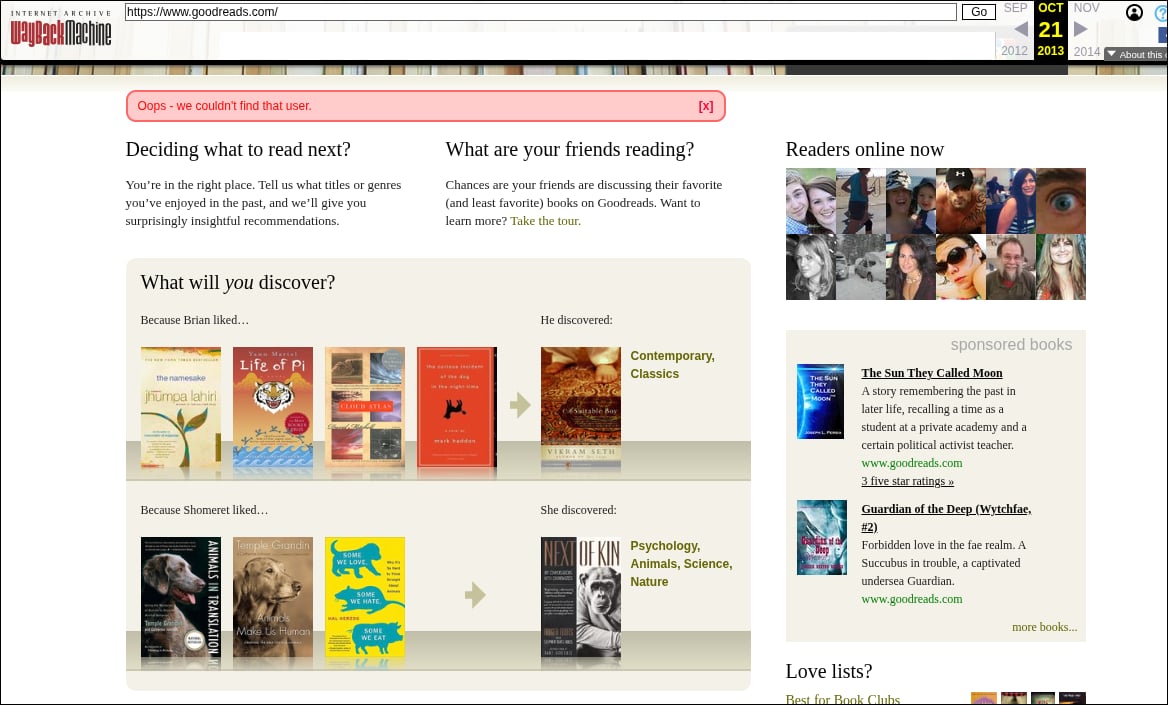
The useful snapshots were:
- 20131021004242
- 20131021111649
From the visible text on those snapshots, I collected the candidate book titles:
- Nudge
- Traffic
- Predictably Irrational
- The Curious Incident of the Dog in the Night-Time
- How We Decide
- The Namesake
- Life of Pi
- Cloud Atlas
- A Suitable Boy
Now the clue made sense. The friend was reading Goodreads on that day, and one of the books shown on the homepage snapshot was likely the key.
Step 4 - Testing the Titles as Vigenere Keys
I normalized the titles by removing spaces and punctuation:
nudge traffic predictablyirrational thecuriousincidentofthedoginthenighttime howwedecide thenamesake lifeofpi cloudatlas asuitableboy
Then I brute-forced them with a small Vigenere decrypt script:
cipher = "WqkickEqtafjosiidgfhjjcbfzjrcatt".upper()
keys = [
"nudge",
"traffic",
"predictablyirrational",
"thecuriousincidentofthedoginthenighttime",
"howwedecide",
"thenamesake",
"lifeofpi",
"cloudatlas",
"asuitableboy",
]
def vigenere_decrypt(ciphertext, key):
key = key.upper()
plaintext = ""
for i, ch in enumerate(ciphertext):
c_val = ord(ch) - ord("A")
k_val = ord(key[i % len(key)]) - ord("A")
p_val = (c_val - k_val) % 26
plaintext += chr(p_val + ord("A"))
return plaintext
for key in keys:
print(key, ":", vigenere_decrypt(cipher, key))Step 5 - Breakthrough
The only clean hit was:
lifeofpi
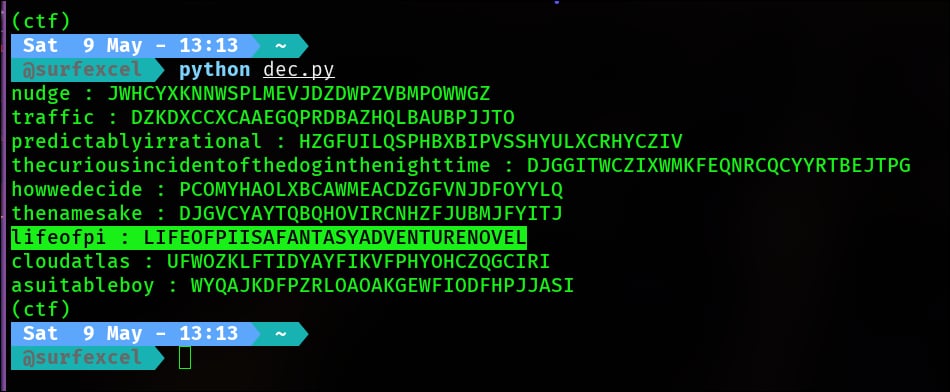
That decrypted the ciphertext to:
LIFEOFPIISAFANTASYADVENTURENOVEL
That was a perfect readable plaintext, so the final flag was straightforward.
Final Flag
ROBOFEST{lifeofpiisafantasyadventurenovel}